I recently had an interesting Problem, regarding the Definition Update Fallback to the Internet on Windows 10 Devices with a managed Windows Defender using ConfigMgr. The Chance that you run into the exact same error is pretty small, however I still wanted to share the Solution.
The Problem
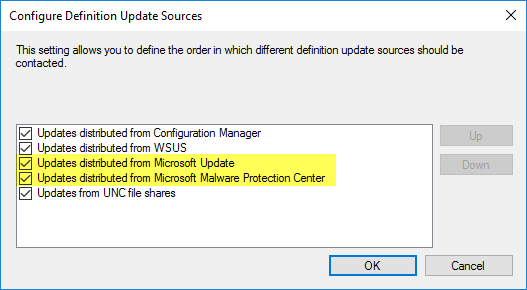
The Fallback to the Internet for updating the Definitions when a Device it out-of-office, is defined by the “Definition Update Sources” in the Antimalware Policy. Here we tell Windows Defender, that it should contact Microsoft Update or the Microsoft Malware Protection Center (MMPC) if ConfigMgr or WSUS aren’t reachable.
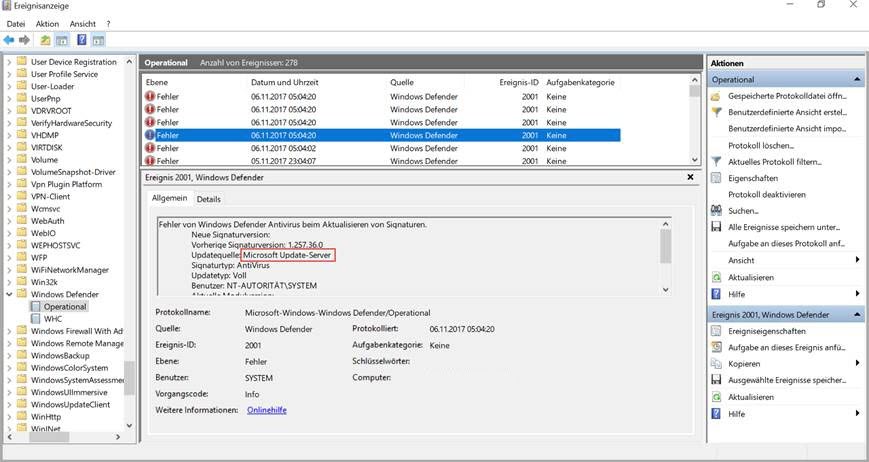
In my Case, I could let a Windows 10 Device on the Internet for days without the Definition getting updated. Looking at the Operational Event Log of Windows Defender, you could see a lot of failed attempts for contacting Windows Update.
The Solution
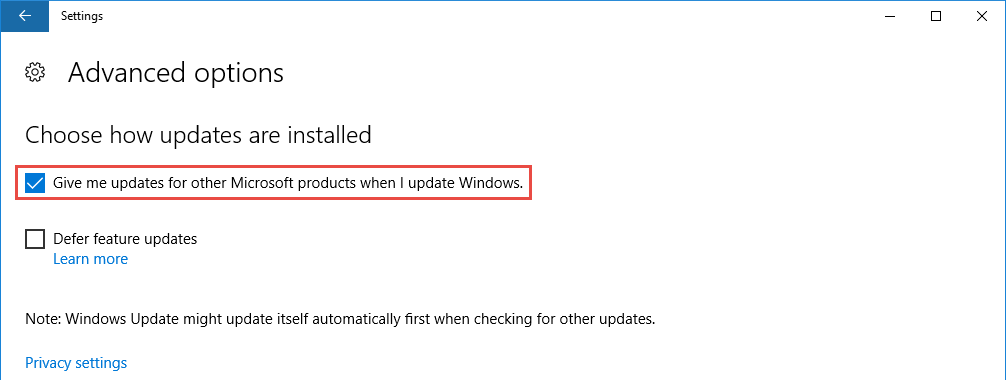
The Solution consists of two steps. First, you need to make sure, that the Option “Give me update for other Microsoft product when I update Windows” is set in the Windows Update Section of the Settings App.
The above option can be enabled during OSD, using the following PowerShell Script:
$obj = New-Object -ComObject "Microsoft.Update.ServiceManager"
$obj.ClientApplicationID = "My App"
# add the Microsoft Update Service, GUID
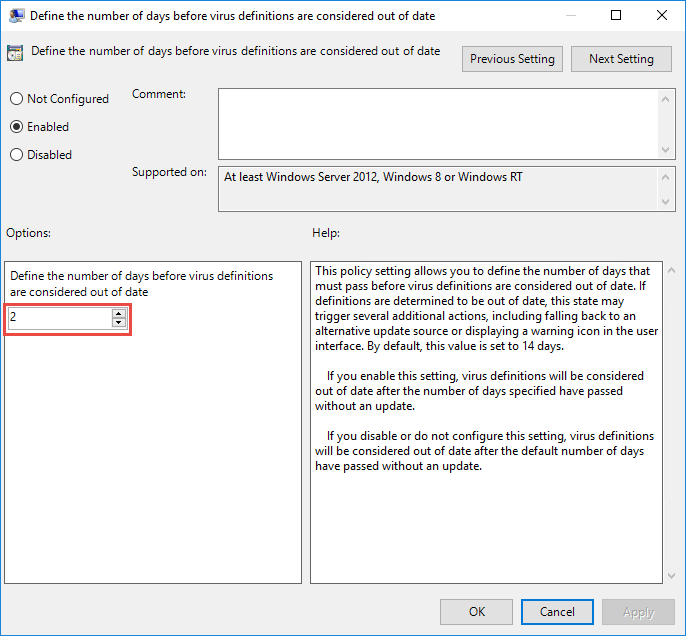
$obj.AddService2("7971f918-a847-4430-9279-4a52d1efe18d",7,"")The Second Setting is to tell Windows Defender the number of days until a Definition is considered out of date. This can be configured using the following two GPO Settings:
Computer Configuration\Policies\Administrative Templates\Windows Components\Windows Defender Antivirus\Signature Updates
– Define the number of days before spyware definitions are considered out of date
– Define the number of days before virus definitions are considered out of date
The lowest possible value here is two days!
After configuring the above settings, the device started to successfully fallback to the Internet for updating the Definitions every two days.